攻击机:
192.168.1.102 Debian
靶机:
192.168.1.2 Windows 7
192.168.1.115 Windows 2003
192.168.1.119 Windows 2003
第一季主要介绍scanner下的五个模块,辅助发现内网存活主机,分别为:
- auxiliary/scanner/discovery/arp_sweep
- auxiliary/scanner/discovery/udp_sweep
- auxiliary/scanner/ftp/ftp_version
- auxiliary/scanner/http/http_version
- auxiliary/scanner/smb/smb_version
第二季主要介绍scanner下的五个模块,辅助发现内网存活主机,分别为:
- auxiliary/scanner/ssh/ssh_version
- auxiliary/scanner/telnet/telnet_version
- auxiliary/scanner/discovery/udp_probe
- auxiliary/scanner/mysql/mysql_version
第三季主要介绍scanner下的五个模块,辅助发现内网存活主机,分别为:
- auxiliary/scanner/netbios/nbname
- auxiliary/scanner/http/title
- auxiliary/scanner/db2/db2_version
- auxiliary/scanner/portscan/ack
- auxiliary/scanner/portscan/tcp
- auxiliary/scanner/portscan/syn
- auxiliary/scanner/portscan/ftpbounce
- auxiliary/scanner/portscan/xmas
- auxiliary/scanner/rdp/rdp_scanner
- auxiliary/scanner/smtp/smtp_version
第五季主要介绍scanner下的三个模块,以及db_nmap辅助发现内网存活主机,分别为:
- auxiliary/scanner/pop3/pop3_version
- auxiliary/scanner/postgres/postgres_version
- db_nmap
第六季主要介绍post下的六个模块,辅助发现内网存活主机,分别为:
- windows/gather/arp_scanner
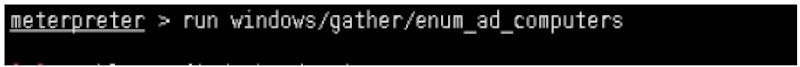
- windows/gather/enum_ad_computers
- windows/gather/enum_computers
- windows/gather/enum_domain
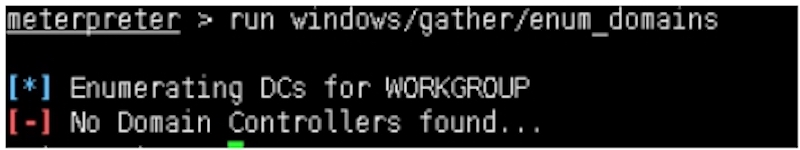
- windows/gather/enum_domains
- windows/gather/enum_ad_user_comments
在实战过程中,许多特殊环境下scanner,db_nmap不能快速符合实战渗透诉求,尤其在域中的主机存活发现,而post下的模块,弥补了该诉求,以便快速了解域中存活主机。
二十六:基于windows/gather/enum_ad_computers发现域中存活主机
二十八:基于windows/gather/enum_domain发现域中存活主机
三十:基于windows/gather/enum_ad_user_comments发现域中存活主机
POST下相关模块如:(列举)不一一介绍
- linux/gather/enum_network
- linux/busybox/enum_hosts
- windows/gather/enum_ad_users
- windows/gather/enum_snmp
至此,MSF发现内网存活主机主要模块介绍与使用完毕。


